The combination of technological advancements and user-centric features positions these platforms as the leading choices for secure and reliable drug trade in 2025. Forums and magazines play a crucial role in keeping users informed about new market links and updates. Platforms like Dread and Darknet Live provide real-time discussions, vendor reviews, and security tips, ensuring users can navigate the darknet safely and efficiently. Pharmaceuticals and recreational drugs remain the most sought-after products on these platforms, with vendors offering a wide range of high-quality substances. The use of encrypted messaging and secure payment methods ensures that transactions remain private and secure, fostering a thriving environment for trade. The dark web marketplace links hold the potential for both risk and reward.
The service retains no copies of any data that passes through a ProtonMail account. Although ProtonMail also exists on the clear web, accessing it via Tor provides an extra layer of privacy if you don’t want to leave a trace of you even using ProtonMail. Fraud-related products, consumer electronicselectronics, self-defense products, and even hosting. Abacus Market, on the other hand, emphasizes privacy and efficiency.
Stay Away From Questionable Sites
Like any other site of such nature, Awazon Market isn’t free from risks, so be careful while accessing it. Since Hidden Wiki maintains all kinds of websites, ensure you don’t open something you don’t want to see. If you choose to visit the dark web, you must take the necessary measures to protect your privacy and security. If you know the right websites, you can easily access a tremendous amount of information, including research articles, news stories, and more. The dark web is a part of the internet that you only step into with a specific tool (Tor, more on this later in the article). Though people usually think of dark websites as the wrong online place, that’s not the complete truth.
For example, it maintains your privacy and enables you to access untraceable content and services. The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s. A network browser gives you access to sites with the ‘.onion’ registry operator.
Facebook is aware of attempts by many governments to restrict access to a tool that allows strangers across the web to talk and collaborate freely. While its .onion address doesn’t make it much easier to maintain an anonymous account, it does make Facebook more accessible in places where it’s censored. One of the most popular ways to get around the dark web is not to use a search engine at all. Just like in the old days of the internet, the dark web maintains numerous indexes of sites, like The Hidden Wiki. Haystak also offers a premium version that allows advanced search, access to historical content, and email alerts. Learn how to automate financial risk reports using AI and news data with this guide for product managers, featuring tools from Webz.io and OpenAI.
- Many dark web search engines are available, and no single option is objectively the best.
- Use strong, unique passwords and store them in a secure manager.
- Discover everything about what is a darknet market, how it works, security threats related to it, and learn how to protect your data online.
- If you must explore sites like The Hidden Wiki, do so with extreme skepticism, never download files, never enter personal info, and never send cryptocurrency to unknown sites.
- To help you make educated choices about cybersecurity to keep you (and your data) safe and secure, by providing detailed, accurate, and practical information based on thorough testing.
- A random dark web link can lead you to malicious software, phishing sites, and illegal content.
The goal is to explain how these domains function, highlight their legitimate uses, and give practical advice for staying secure. ASAP is a tech nerd’s playground—accepting BTC, LTC, ZCash, and Monero, it’s got options for days. Listings aren’t public, but it’s steady—think drugs (weed, pills, some synthetics), a few digital extras like cracked accounts. They’ve got 2FA and encryption that’s tighter than a drum, which I’ve tested against crash-prone sites and found solid.
Can I Use Tor To Browse The Surface Web?
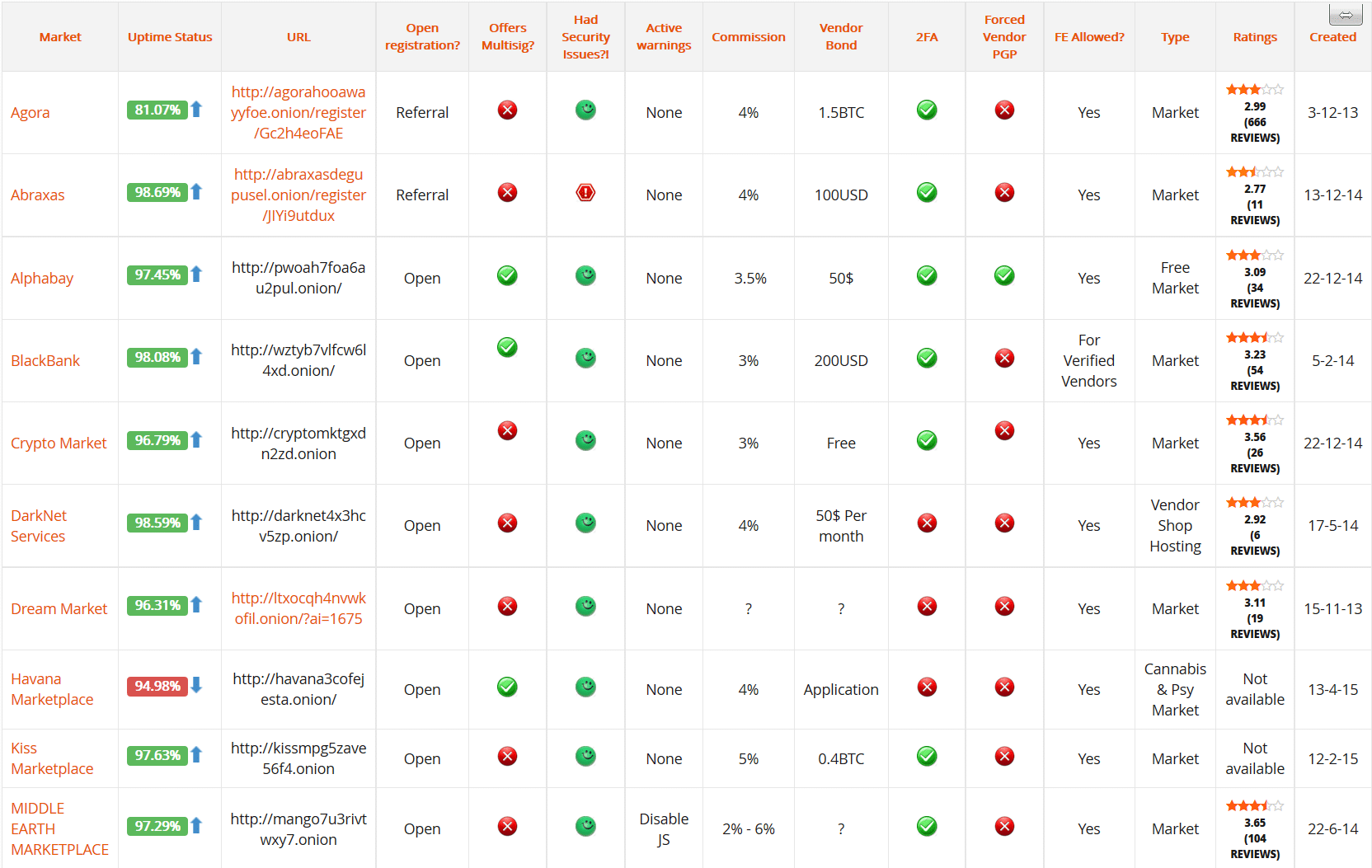
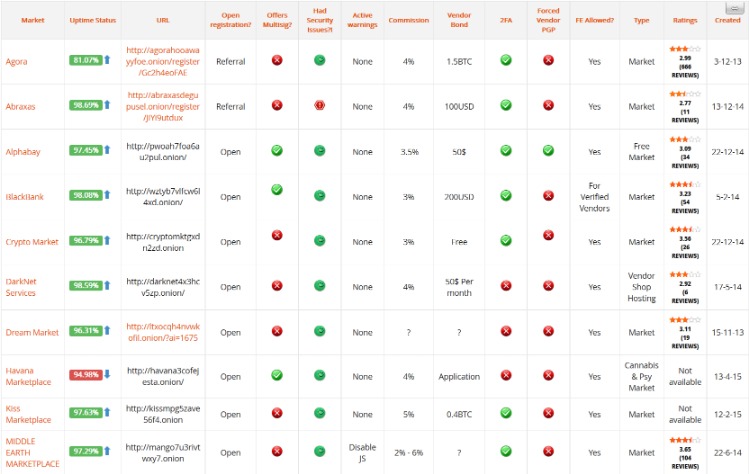
Darknet market lists play a crucial role in simplifying access to these platforms. By aggregating verified links and providing up-to-date information, these lists reduce the time users spend searching for reliable markets. They also include user reviews and ratings, helping newcomers identify trustworthy vendors and avoid scams.
Finding A Silk Road Alternative: What Are The Best Options Today?
Data gleaned from ransomware and data breaches is available on the dark web. Millions of customers’ personal data, including names, addresses, bank account and credit card account information, and many other forms of sensitive data. The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information.
Secure Communication And Collaboration Tools
- This use of cryptocurrency makes transactions fast and secure, and it supports the overall goal of privacy on the dark web.
- It is also used by whistle-blowers, journalists, and other individuals who are not involved in illegal activity but need to protect their communications and identities.
- Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there.
- It’s picking up steam fast, and I’d keep an eye on it if you like a community feel.
- Small details—like time zones, browser language, or file properties—can give away identity.
Navigating dark web marketplace links can be risky; however, with the right tools, you can explore safely. Naturally, this makes the dark web a breeding ground for illegal activity. But onion sites can also serve nobler goals, like providing access to information and independent journalism in countries with government censorship. A VPN protects your connection against everyone, not just your ISP and the authorities. This process also prevents your ISP from seeing your data or where it’s going. Since the ISP can’t detect you’re accessing dark web URLs, it won’t trigger any alarms about your online activity.
mark it means it has been verified as a scam service and it should be avoided. Radar Rundown The dark web consists of many websites with uncensored information; choose a suitable … There are several other browsers you can use, such as Freenet and I2P, but Tor is the most recommended option. In this era, it takes one wrong click and all your sensitive data ends up in the wrong hands.|Perhaps the best-known thing you can buy on the Dark Web is information collected in what seems like the almost daily data breaches we read about in the news. That information can include checking and credit card account numbers, social security numbers, and other sensitive information. You don’t need special tools or a special browser like you need to access the dark web (more about that later). Anyone can access the deep web by using specialized search engines, dedicated web directories, and other sources that can help you find the data or information.|The site’s easy to use, with filters that actually work and a forum where folks swap tips. Vendors get checked hard using Recon, so scams aren’t as common. Word is, they’re pushing digital goods big-time next year—think stolen logins and cracked software. On these markets, you can find a variety of goods and services, ranging from legal items to illegal ones such as counterfeit passports, narcotics, and hacking tools.|We review and list tools and products without bias, regardless of potential commissions. To help you make educated choices about cybersecurity to keep you (and your data) safe and secure, by providing detailed, accurate, and practical information based on thorough testing. Yes, you can access the dark web on mobile — you just need the right app. Android users need to download the Tor Browser app, while iPhone fans should get the Onion Browser app. That’s why it’s important to verify links through trusted directories and proceed with caution.|For a number of technical reasons, it’s much faster and more reliable than Tor. The peer-to-peer routing structure is more advanced, and it does not rely on a trusted directory to get route information. I2P uses one-way tunnels, so an eavesdropper can only capture outbound or inbound traffic, not both. The big downside is that your ISP will know you are using Tor, which is cause for concern in some places and will put many people off using this method. In this instance, too, it is important to use a logless VPN and pay with Bitcoin if you can to stay anonymous. The VPN over Tor technique is also susceptible to an end-to-end timing attack, though it’s highly unlikely.}
Protecting Against Malware And Exploits
The U.S. Naval Research Laboratory developed onion routing as a method to secure intelligence communications. By wrapping data in multiple layers of encryption and sending it through volunteer relays, the system hid both the sender and receiver. By the early 2000s, the project became public as The Tor Project, which still publishes official documentation to help users understand and configure the network. Abacus Market excels not just by facilitating smooth transactions, but by prioritizing user experience with a user-friendly interface and effortless navigation. The forum integration encourages an active community where users can exchange valuable knowledge and insights, fostering a sense of belonging.
Do I Need A VPN If I’m Already Using Tor?
Platforms like SecureDrop allow these carriers of truth to evade tracking. It protects their submissions using high-end encryption and doesn’t log their IP addresses or device information – full anonymity. Onion sites are far safer to use as they are hidden deep within the deep web. Also, since users can only access them using the Tor browser (with its high-end encryption), users can be rest assured their identities and locations remain hidden. Silk Road was one of the first darknet markets, but in 2013, the FBI shut it down.
Bitcoin Powers Secure And Private Trade On The Darknet
Using unique keys for each vendor or market prevents leaks and protects your communication from third parties. Use the Tor Browser with all security settings enabled, combine it with a trusted VPN for additional privacy, and always keep your browser and operating system updated. Riseup is an invite-only email and communications service that doesn’t hold onto any of the data you generate when you use it. It describes itself as a tool for social change and “a project to create democratic alternatives.” Riseup requires you to have the onion link as well as an invitation.
Top Dark Web Marketplaces Of 2025: A Deeper Dive Into Illicit Trade Markets
It’s a hidden collective of sites that you could only access through a special browser. Since all activity on the dark web is anonymous by default, it is definitely where the murkiest transactions on the internet take place. A study by researchers at King’s College London that examined the contents of over 2,700 darknet sites found that approximately 60% of them hosted illicit content. To make its journalism more accessible to readers around the world, the New York Times launched its onion service in 2017. Beginning in September 2021, Abacus Market has established itself as one of the leading dark web marketplaces. After AlphaBay closed, Abacus Market took its place as the world’s largest underground darknet marketplaces.
As of 2020, nearly 57% of the dark web was estimated to contain illegal content, including violence and extremist platforms. The dark web marketplaces are mainly defined into two categories. When you use it, all the web traffic automatically routes through Tor. If the operating system detects any non-anonymous connection, it blocks it, thus ensuring maximum online protection.