A curated collection of darknet resources for educational purposes, offering insights into darknet frameworks, tools, and security practices. This encrypts your communications with websites, providing an additional layer of security. You can use the HTTPS Everywhere extension, which comes pre-installed with Tor Browser, to automatically enforce secure connections whenever they are available.
Swap Data In Countries That Censor The Internet
Best of all, Digging the Deep Web is written in plain, easy-to-understand English, and you can read it in one sitting. Essentially, this 320-page book takes you into the murkiest depths of the dark web. It is little wonder that Silk Road is one of the best dark web books to read today. Ormsby expertly told the story of the Silk Road’s rise and fall with deep insights into the world of the dark web. The author is no stranger to the dark web, as her research of the darkest web has led to hack attempts on her computer and death threats. The official website of Archetyp Darknet Market, this website was created by the Archetyp Team to distribute trust onion links and URLs and publish articles about Archetyp Market.
Dark Web Tools And Services

As MGM Grand nears its two-year mark at the time of writing this guide, it’s enjoying a surge in popularity, partly due to the recent unavailability or closure of several major competitors. Users have given the market positive reviews, citing its competence and trustworthiness. However, it seems to place a considerable amount of security risk on its users, given its lack of support for XMR, use of static BTC addresses, and absence of mandatory PGP encryption or 2-FA. Despite these concerns, MGM Grand has been running smoothly without any interruptions or downtime, amassing a significant user base. Overall, the MGM Grand is a noteworthy darknet market that presents a distinctive amalgamation of advantages and limitations.
Why Do The Darknet And Deep Web Exist? Legitimate Uses
Think of it as the courier handing your unsealed letter to the recipient’s mailbox.
How To Protect Your Data From The Dark Web
This book is a great choice if you want a detailed tutorial on how to use Tor for the dark web. It takes you through the setup and how to use the software to evade surveillance by prying eyes. Award-winning journalist Evan Ratliff spent nearly five years piecing together the uncommon story. The Goodreads community has responded well to the riveting account of a crime boss with thousands of positive reviews, and it’s no secret why the book tops our list.
Purchase Legal Goods Secretly
- Also, set up two-factor authentication (2FA) to add an extra layer of protection in case someone manages to figure out your password.
- The significance here lies in the potential damage to individuals and businesses.
- We’ll navigate this intricate maze with you, uncovering its secrets while ensuring your online safety.
- Always remain vigilant about the risks involved with risky behavior, even when browsing through Tor.
- Dark markets include features similar to those found in legitimate e-commerce platforms, such as product listings, user reviews, ratings, and customer support.
If your personal information has been leaked on the dark web, your risk of identity theft and financial fraud significantly increases. This is why many people prefer an identity theft protection service and a financial and credit fraud protection solution. Anonymity on the dark web may be attractive to government critics and victims of harm who want to keep their identities private. However, criminals and malicious hackers also use the dark web to hide their illegal activities. Such sites include blogs, gaming sites, social media, and super-encrypted email platforms. However, it’s illegal if you venture into the dark web to commit unlawful actions such as downloading child porn, buying fake documents, drugs, credit cards, and more.
How To Access The Dark Web Safely
However, today’s most popular search engines — including Google, Bing, and DuckDuckGo — only index a portion of the internet. Our goal is to deliver the most accurate information and the most knowledgeable advice possible in order to help you make smarter buying decisions on tech gear and a wide array of products and services. Our editors thoroughly review and fact-check every article to ensure that our content meets the highest standards. If we have made an error or published misleading information, we will correct or clarify the article.
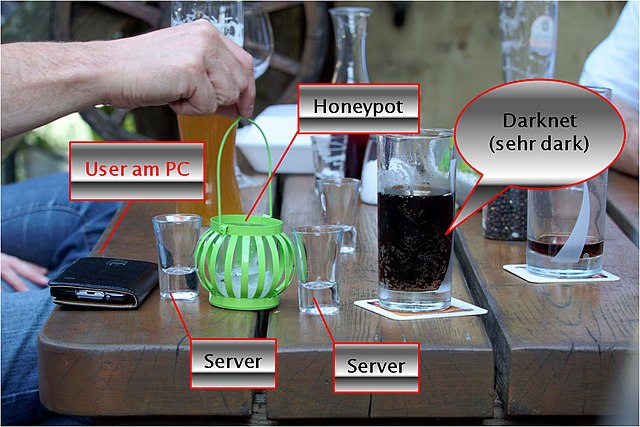
Instead, it’s wrapped in several layers of encryption and sent through a chain of at least three relays. The deep web is just the part of the internet you can’t find with a search engine. It’s not mysterious or spooky; it’s home to everyday things like scientific research, medical records, private financial information, and secure communications. The technology behind this anonymous connection is known as “onion routing,” which utilizes a layered approach to obscure data and protect users’ locations on the network.
SECURE OPERATING SYSTEMS
The dark web wasn’t the invention of a single individual but from efforts to build secure, anonymous communication. Its foundation is the Onion Router (Tor) project, developed in the 1990s with funding from the U.S. Naval Research Laboratory to protect sensitive government communications. Later released as open-source, Tor became accessible to the public, enabling anonymous browsing for activists, journalists, and everyday users—while also giving rise to today’s dark web. Traditional social media platforms such as Facebook have also created versions that work with the dark web to provide services across all dimensions of the World Wide Web. However, unlike Facebook, the DWSN requires users to remain anonymous and not reveal personal information to protect their privacy.
- Everything is in English, but users from around the world are welcome.
- Keep in mind that those links won’t work unless you’re accessing the Darknet through the Tor Browser.
- With the current technology, cyber terrorists can exploit their weaknesses to carry out attacks.
- Tools like Tor are used to bypass government-imposed firewalls and surveillance, ensuring open communication.
MGM is a captivating destination for those looking for an exciting and evolving exploration into the digital depths. You face significant risks when using dark markets, including scams where vendors take payment without delivering goods. There’s high exposure to malware and cybersecurity threats that can steal your personal information. Law enforcement agencies actively monitor these markets and can track users despite anonymity measures.
It can only be used to access the content uploaded to the Freenet, which is a peer-to-peer distributed data store. Once you upload something, it stays there indefinitely even if you stop using Freenet, so long as it is popular. After all, it’s much less popular, can’t be used to access normal websites, and isn’t as easy to use, among other disadvantages. Both rely on a peer-to-peer routing structure and layered encryption to make browsing private and anonymous.
This short book by AJ Wright is a basic guide for people who want to know how the dark web works, including the excesses and positives. It explores the origins of the dark web, the deep web, and the technologies that support them. The Dark Net is not one of those dark web books that go on and on about how the dark web is bad. The book explores the dangerous and the good sides, making for a balanced read. Jamie Bartlett, a journalist, interviews various victims for this book to uncover the light-less world of the dark web.



