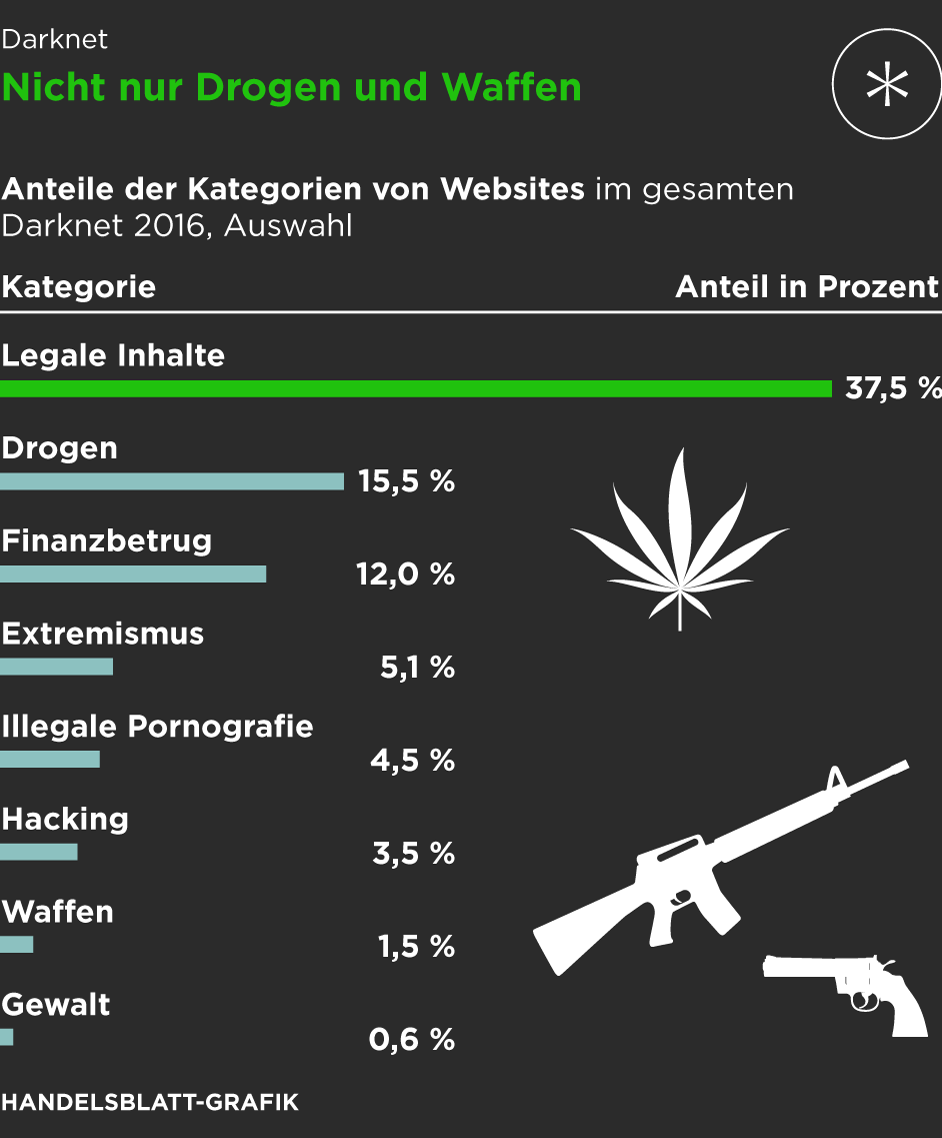
Their presence can make you wonder why darknet markets and not just the regular online stores. Dark web markets have exploded in scale and reach in 2025, becoming the most dangerous hubs for trading drugs, stolen data, and hacking tools. These anonymous marketplaces—operating mainly on the Tor network—are now a primary threat vector for businesses and cybersecurity professionals. In recent years, some darknet markets and fraud shops have been integrating crypto payment processors on their websites via APIs, possibly as a way to improve operational efficiency and increase security.
Data Sources

However, the evolution of the S2S network shows a different pattern than that observed in both the multiseller and the multibuyer networks. Violations of OFAC regulations may result in civil or criminal penalties. The months and years after Silk Road’s closure were marked by a greatly increased number of shorter-lived markets as well as semi-regular law enforcement takedowns, hacks, scams and voluntary closures. Start with verified directories like Ahmia or Hidden Wiki, use a secure environment (VM + VPN + Tor), and stick to ethical, research-oriented content only. Use a VPN, access the dark web only through the Tor browser, avoid logging in with personal credentials, and use virtual machines for isolation.
The Importance Of Verified Onion Links
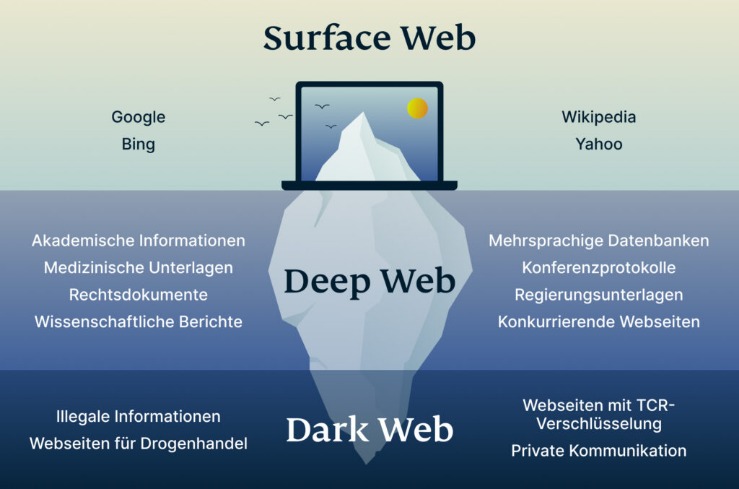
Dark Web marketplaces are much like ecommerce websites on the Surface Web, but with one major difference — they mainly sell illicit and/or illegally obtained goods. These include stolen login credentials, credit card details, medical records, and cryptocurrencies. According to the latest available data, Dark Web marketplaces have at least half a million users with more than 2,400 sellers.
- The BBC news website has a special .onion site, which you need to access via the dark web.
- These attacks often include stealing victims’ data and threatening to release it on the dark web if the ransom isn’t paid.
- Keep in mind that you’ve to use very specific keywords when searching.
- It enhances buyer transparency by importing vendor feedback with PGP proof.
- Individually, they are able to yield significant high incomes compared to other types of sellers.
How Do I Verify A Darknet Market Link Is Legitimate?
For example, during the Russian-Ukraine conflict, citizens used dark web versions of social media to share information when traditional access was blocked. When AlphaBay became inaccessible as a result, thousands of its buyers and vendors flocked to the then law enforcement-ran Hansa market to continue their operations. Dutch police, operating servers across the Netherlands, Lithuania, and Germany, capitalized on the eight-fold surge of users visiting the market in the weeks following. The authorities used the time to gather information on high value targets and identified delivery addresses for sizable orders, passing along 10,000 international addresses of buyers to Europol. Dark web commerce sites have the same features as any e-retail operation, including ratings/reviews, shopping carts and forums, but there are important differences. When both buyers and sellers are anonymous, the credibility of any ratings system is dubious.
Therefore, you need to start by changing your passwords, and you need to notify your credit card or bank provider. STYX market features a robust verification process, making it look more exclusive. In fact, they have a Telegram channel to offer users with live updates.
How To Protect Your Personal Data Online
However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. These sites aren’t just important resources; they’re like lifelines used to serve readers living under oppressive regimes. As listed above in our article, even respected organizations like the BBC and ProPublica have a version of their site on the dark web.
Our Network
We can inform you about breaches that have resulted in your information; we can help you understand your needs to help mitigate risks; and we can recommend tools to make it easier to protect your information online. If, for example, a breach exposed your financial information, you’ll need to check your bank statements for any suspicious transactions. In addition to its emphasis on stolen credentials, 2easy Market offers a variety of cybercrime tools, such as hacking services, exploit kits, and other resources for conducting cyberattacks. Silk Road, which emerged in 2011, combined TOR and bitcoin to become the first known darknet market.
There are some things that you can’t find on the surface internet but are available in the darknet markets. Therefore, it’s almost impossible for authorities to track those who run the darknet markets or even their locations. Accessing darknet markets safely isn’t just about the tools you use — it’s also about the way you behave online. By following simple but effective OPSEC strategies, you can protect your identity, avoid scams, and reduce unnecessary risks.
The chart above shows that, while values haven’t risen back to 2021 levels, darknet market revenue has slightly rebounded since Hydra’s closure in 2022. Sadly, the answer is no—it’s not possible to scan the entire dark web. While some companies do offer this service, be aware the results are always incomplete, because there are many private forums and sites that simply cannot be discovered or indexed by a scanner. Let’s look at how criminals are using the dark web in 2023 and identify dark web trends so that cybersecurity teams can hone our techniques and defend effectively. DeSnake joined the conversation, creating an account with his moniker on September 12, 2021 in attempts to mitigate the marketplace’s potential reputation damage.
Use Active Monitoring Of Financial And Identity Theft
Various cryptocurrencies such as Bitcoin and Monero can be used to make purchases. Never log in with your real name or reuse passwords from other accounts. Stick to cryptocurrency, avoid downloading anything, and don’t share any personal info. Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement. For instance, cybercriminals can buy credit card details with a $5,000 balance for just $110. Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools.

Awazon Market is a top-tier dark web marketplace with claims to revolutionize secure anonymous commerce. It offers a wide range of goods and services with robust anti-DDoS protection (with military-grade security protocols) and no JavaScript, ensuring privacy and uptime. This guide outlines different ways of safely accessing dark web stores and the list of reliable dark web marketplaces you can consider visiting in 2025 for research and monitoring purposes.
Patterns recommended to avoid include hiring hitmen like Dread Pirate Roberts, and sharing handles for software questions on sites like Stack Exchange. One of the central76 discussion forums was Reddit’s /r/DarkNetMarkets/,777879 which has been the subject of legal investigation, as well as the Tor-based discussion forum, The Hub. Yes, platforms like DeHashed, LeakLooker, and DeepPaste provide access to data breaches and leaked credentials. The Tor browser is a privacy-focused web browser that allows users to browse the internet anonymously, including accessing .onion domains on the dark web. While the dark web is not illegal, mainstream awareness of the darknet is tied to the rise of the Silk Road, an online black market founded in 2011 by Ross Ulbricht.
Then, we investigate both market star-graphs and user-to-user networks, and highlight the importance of a new class of users, namely ‘multihomers’, who operate on multiple marketplaces concurrently. Specifically, we show how the networks of multihomers and seller-to-seller interactions can shed light on the resilience of the dark market ecosystem against external shocks. Our findings suggest that understanding the behavior of key players in dark web marketplaces is critical to effectively disrupting illegal activities.
The market emphasizes anonymity and security, conducting transactions exclusively through cryptocurrencies like Bitcoin and Monero. FreshTools, founded in 2019, specializes in selling stolen account credentials and data, particularly webmail, RDPs (Remote Desktop Protocols), and cPanels. The marketplace requires merchants to pay fees to sell their products, helping ensure a certain level of quality control. Changing the Tor browser settings can further boost your security levels on the dark web shops.



