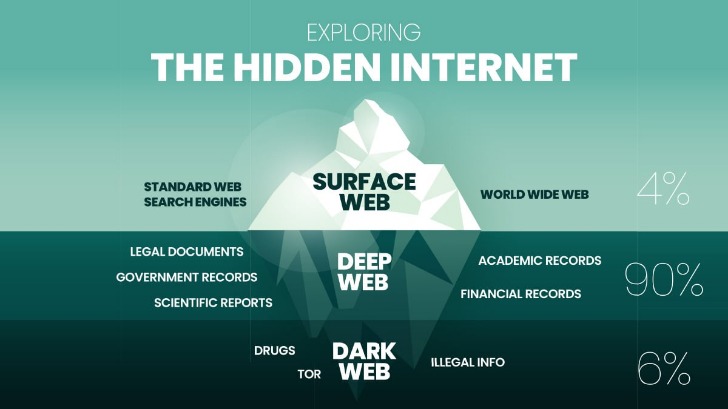
Beneath it lies a hidden world, a digital underground where criminals trade stolen data, hackers sell exploits, and entire marketplaces exist beyond the reach of traditional law enforcement. The difference between the dark web and the deep web is that the deep web refers to websites and web pages that aren’t indexed by search engines, like login pages and payment portals. The dark web, by contrast, is configured on darknets — online networks that can be accessed only with special software and techniques. The deep web is significantly larger, accounting for approximately 90–95% of online content. Unlike the surface web, it consists of pages not indexed by standard search engines.
VPNs are often recommended as protection in such cases, but Whited disagrees. Indeed, Facebook, The New York Times and now even the CIA have sites on the dark web, hosting “onion” versions of their pages that can be accessed via the Tor browser. The spy agency is hoping to securely and anonymously collect tips, though its entire website, including job listings, are available on the onion service.
Tips For Safe Access To The Dark Web
While ad blockers can prevent most harmful links from loading, you should also take steps to protect yourself from malware to keep your data safe from hackers and scammers. Whilst using Tor isn’t illegal, the encrypted data packets it uses make it fairly easy to detect. Given its relationship with crime, some ISPs and companies automatically block Tor traffic. Even if such sites were blocked from the regular open web, anyone using the Tor Browser could still access their email using the .onion addresses.
Agentic AI–Driven Threat Intelligence Tailored For Every Function
For those who really want to explore the dark web, several pages called the Hidden Wiki serve as a directory of links to other .onion sites. You will never know when you stumble upon illegal materials, inadvertently download malicious software, or expose yourself to identity theft. But if you must visit the dark web for ethical reasons, here are some safety precautions. The Deep Web includes unindexed content like private databases and password-protected sites accessible with standard browsers. The dark web hosts various types of illegal content, such as stolen data, child exploitation material, and prohibited items. As an average Internet user, you may accidentally stumble upon such content.
Data breaches happen all the time, and your login credentials and other data might be on the dark web already. Avast BreachGuard scans the dark web and will alert you immediately if and when it detects your personal data. BreachGuard will guide you through the process of recovering your accounts, helping you lock them down before a hacker can use your leaked credentials. Later, Tor’s underlying code was released under a free license, and a nonprofit called the Tor Project was formed. In 2008, the Tor Browser was released, which made it easy for anyone to get on the darknet.

There are also dark web search engines, like Torch, that allow you to search for some types of dark web content. You won’t always get the search results you expect, however, as the dark web doesn’t index like the clear net and many websites don’t want you to find them. As mentioned above, some major clean net sites also maintain a dark web site. This is to make sure people living under restrictive governments can still access uncensored news, social media, or other important online services. Some major websites also operate dark web versions, such as Facebook, the BBC, and ProPublica. Sites like these let users access services without running into censorship, protecting user identity while visiting potentially restricted information.
Risks Associated With The Dark Web
The dark web didn’t start as a haven for cybercriminals – it was actually developed for a very different purpose. Originally created by the US military to enable secure and anonymous communication, this hidden layer of the Internet has since evolved into a complex digital underground. The content management system into which I am typing this article is on the Deep Web. Meanwhile our company intranet is hidden from search engines, and requires a password.
Securing Your Digital Presence: Final Thoughts On The Dark Web
Ransomware as a service, stealer malware as a service (SMaaS), and phishing-as-a-service operations are thriving and helping fuel illicit add-on services. There are also myriad support services that help lower the barrier to entry in executing these attacks, or to help make attacks more efficient. These include crypting services, dropper services, and exploit kits for RaaS and SMaaS, according to Carroll. I don’t recommend seeking out dark web content unless you have a specific reason to do so. If you want to observe the lawless sides of the internet from afar, check out YouTube videos of dark web explorations, like this one from John Hammond, to satisfy your curiosity.
Legal Uses Of The Dark Web
Individuals can access the dark web by installing specific, anonymous browsers, such as TOR. Once installed, the browser works the same as a traditional browser. However, it can be hard to find information because the dark web doesn’t use an index to locate the desired information. Users will also notice that dark website addresses end with the .onion extension rather than the traditional .com, .org, or .edu. Users should install security software to keep their computer and personal information safe. The dark web’s anonymity accommodates illegal activity and contributes to its reputation as being a haven for criminals.
What Will You Find On The Dark Web?
Tools like Tor anonymize users by masking their IP addresses, but this doesn’t make them invisible. On the other hand, it hosts illegal activities like black markets for drugs, weapons, and stolen data. While not all use is unlawful, its anonymity makes it a hub for actions that are harder to trace on the regular internet. Because it’s anonymous by design, it attracts a lot of shady activity. You’ll find scams, fake sites, and illegal content in some corners, and stumbling into the wrong place can put your device or identity at risk. There’s also the danger of accidentally downloading malware or clicking on phishing links that try to steal your personal info.
Using the ProtonMail .onion site offers security and privacy advantages. Moreover, the company also uses HTTPS and SSL encryption on the Onion site for extra protection. This makes it even harder for third parties to see your email traffic. The website has an advanced search filter and an easy-to-use interface, which makes it easy to find what someone is looking for.
Bitcoin Services
Therefore, it is important to be mindful when using the dark web to ensure that it is being used for legitimate purposes. In this section, we’ll delve into the darker side of the dark web and explore the various illicit activities that take place there. Private Internet Access has 10+ years of experience leading the VPN industry. With a strict no-logs policy, world-class server infrastructure, and transparent open-source software, PIA prioritizes your online privacy, security, and freedom above all else.
Use A Reliable VPN For Anonymity
Tools like Norton 360 are critical on the dark web because they actively scan for and block threats — ensuring your device remains secure even in the dark web’s riskier environment. This added protection is vital, whether you’re using the dark web for privacy or out of curiosity. Additionally, a VPN like ExpressVPN masks your IP address before entering the Tor network, making it harder for your internet provider to detect Tor usage.
- You will never know when you stumble upon illegal materials, inadvertently download malicious software, or expose yourself to identity theft.
- It is also used to gain access to private networks and bypass censorship imposed by governments and educational institutions.
- Since using Tor can itself draw suspicion, a VPN masks the fact that you’re using it.
- While not all use is unlawful, its anonymity makes it a hub for actions that are harder to trace on the regular internet.
- If the Tor browser is running, you can immediately check whether it is working as intended.
- Addresses also change frequently due to the transient nature of many dark web actors.
Risks And Challenges Associated With The Dark Web

The concept of an encrypted, hidden layer of the internet began taking shape in the 1990s. The U.S. Naval Research Laboratory developed the precursor to the Tor (The Onion Router) project during this period as a means to protect government communications. Drugs are typically sold using cryptocurrency to maintain anonymity, and the buyers and sellers are often difficult to trace. These markets operate similarly to physical drug markets but are hidden from law enforcement through the use of the Tor network. Some dark websites serve as platforms for whistleblowers to anonymously share sensitive information. Examples include SecureDrop and GlobaLeaks, which are used by journalists and activists to securely receive documents and tips.
Despite the ominous-sounding name, the Dark Web leverages encryption, volunteer relay nodes, and hidden domain systems that do not conform to conventional address resolution. Such architecture helps websites and services obscure their physical server locations. Cybersecurity risk assessments and regular monitoring of dark web activities are essential to identifying and mitigating threats before they result in significant damage. Onion routing encrypts data multiple times before sending it through a series of volunteer-operated servers, called nodes or relays. Each node decrypts one layer of encryption and passes the partially decrypted data to the next node. This procedure proceeds until the final node, referred to as the exit node, removes the final layer of encryption and transmits the request to its intended destination.



