
If you ever decide to explore the dark web, protecting your identity is crucial. Most people start by using the Tor Browser, which hides your IP address. Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools.
More Forums
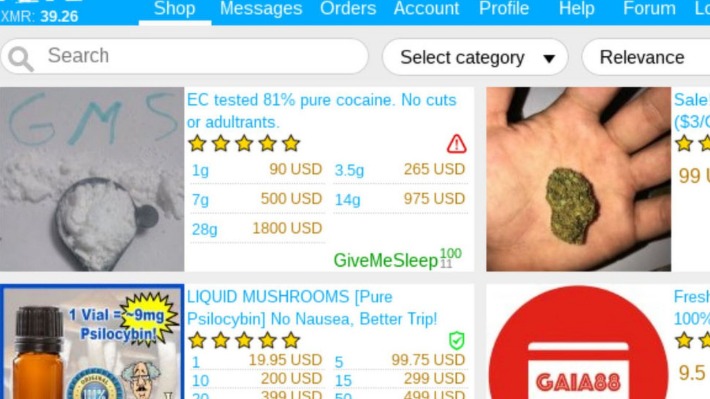
One of the most common types of illicit goods is stolen login credentials, often collected from data breaches. These “credential dumps” allow criminals to access online accounts, steal identities, and commit fraud. Law enforcement agencies monitor many dangerous markets, and even anonymous browsing isn’t foolproof. Just visiting these sites can attract attention from law enforcement, especially if you interact with known vendors or download suspicious content. Even if you’ve never visited these markets, your personal and financial data might already be there, having been leaked through a data breach. Criminals use this information for money laundering, opening bank accounts, applying for loans, and draining your finances.
- Some marketplaces provide an escrow service for participants in a transaction in exchange for a fee.
- When it opened, Silk Road apparently prohibited the sale of anything with the intent to “harm or defraud,” such as child pornography, assassinations, or weapons.
- Hence, we also gathered snapshots of 5 underground marketplaces and 6 forums collected by the anonymous marketplace archives programs and previous research projects 20.
- With the advent of crypto-currencies, it became not only possible to complete trades online without leaving a money trail but easy.
Agentic AI–Driven Threat Intelligence Tailored For Every Function
Last but not least important, if you get caught red-handed with a package containing controlled substances delivered from abroad, you’ll be charged with drug smuggling. While receiving national shipments, you face simple possession or possession with intent to supply charges (depending on the drug quantity). Let’s get this straight — not everything on the dark web is illegal or harmful.
We use data of DWM transactions on the Bitcoin blockchain pre-processed by Chainalysis Inc. Although other coins are used, such as Monero recently, Bitcoin is still the mostly used in the ecosystem, being supported by more than 93% of markets7,9. The pre-processing relies on established state-of-the-art heuristics to cluster addresses into entities, such as cospending, intelligence-base, and behavioral clustering39,40,41,42. The resulting data set includes for each transaction the source and destination entities, the time, and the value of the transaction. The number of sellers in each category and multisellers as a function of time is shown in Fig. Until the end of 2013, when Silk Road is the dominant market (see Fig. 3), market-only sellers is the dominant category, and there are no multisellers.
Essential Security Measures
- Torzon Darknet Market offers a unique premium account feature and a raffle system for potential buyers.
- “Bravo,” says another for a $5 sample of fentanyl, one of 18 reviews posted on the product’s profile page in the last week.
- While receiving national shipments, you face simple possession or possession with intent to supply charges (depending on the drug quantity).
- This information is then processed to generate an index of average prices for a broad range of specific products.
- Its USP was its consistent uptime and a well-maintained community of verified vendors.
Dark web markets are home to a billion-dollar industry dealing in illicit goods. Unsettling dark web facts like this make them a great concern for governments. US agencies, like the FBI, are constantly working with international law enforcement groups to stop the growth of dark web markets around the world. IN OCTOBER 2013, Ross Ulbricht was arrested by the FBI and charged with money laundering, conspiracy to commit computer hacking and conspiracy to traffic narcotics. Two years earlier, Ulbricht had launched the Silk Road, the first modern dark web market, known for selling drugs that are illegal in the US.
Recent Posts
The website allows a personalized searching experience, where you can search according to your geographical location, country-specific, and keyword or price-specific search results. As long as there remains supply and demand for illicit goods, it seems that Darknet markets will continue to exist. Some imitate Silk Road (there was even a “new” Silk Road market operating for a while), while others find ways to innovate.
Transactions can be made using Bitcoin or Monero, and the platform keeps users in the loop through an official Telegram channel. It also requires users to verify their identity carefully to build trust with buyers focused on fraud. These marketplaces operate much like traditional e-commerce platforms, but instead of gadgets and clothes, you’ll find listings for illicit goods and services from stolen data and counterfeit documents to banned substances. In this blog, we’ll unpack what dark web marketplaces are, how they work, why Bitcoin plays a central role, and which platforms have gained popularity. Our study used opioid keywords and jargons to recognize listings and forum traces related to underground opioid trading activities.
ASAP Market (Best For Drug-Free Listings)
But don’t expect the dark web’s downtime to last, says Roman Sannikov, an analyst at security firm Recorded Future. “My guess would be the lower-tier markets just grow in prominence again,” he says. But despite those wins, a years-long war of attrition seems to be exactly the pattern that the dark web’s booms and busts now follow, argues Carnegie Mellon computer scientist Nicolas Christin, a longtime dark web researcher. In an economy where the demand—drug-addicted users—remains constant or growing, that’s only to be expected. On the dark-web drug market Empire this week, business proceeds as usual.
Steps To Get In

It’s also super important to train employees to spot phishing attempts and other cyber threats. Investing in threat intelligence services can help by keeping an eye on potential risks and providing insights into new threats. Businesses have plenty of opportunities to fortify their defenses against the lurking threats of the dark web. First off, ramping up their cybersecurity efforts is a must, which means setting up strong firewalls, keeping software up to date, and using multi-factor authentication (MFA) to add extra security. The risk of data breaches is higher than ever for businesses, potentially leading to financial loss, reputational damage, and legal consequences. Individuals are also at risk, as their personal information can be exploited for identity theft or sold multiple times over.
Lessons From Dark Web Marketplaces Ecosystem
Run a dark web scan and you may be surprised to find your own personal data up for sale. When the Silk Road was in operation, you could search for the Silk Road link on Tor, then redirect to a signup screen requiring a username and password. Suddenly, users could order any illicit substance they wanted from dealers online and have it delivered, no questions asked, to their homes by the US Postal Service the very next day. Only, these industrywide best practices will make illegal online trades even harder to track for law enforcement.
Ready To Explore Web Data At Scale?
The list of dark web markets closed just in recent years is extensive, including Dream, WallStreet, White House, DeepSea, and Dark Market. Although law enforcement certainly have to play Whac-A-Mole with such sites, with new markets springing up as soon as established ones are closed, doing so makes it harder for buyers and sellers to build steady businesses. Law enforcement agencies have been making significant strides in taking down major dark web marketplaces in recent years.

The selection depends on the marketplace, and not everything found is legal. It has built a reputation for being a reliable source of stolen credit card data and PII. Renowned for its extensive inventory of financial data and sophisticated operating methods, Brian’s Club is a key player in the underground economy of financial cybercrime. The dark webmarket saw a rise in posts related to stealer malware, designed to pilfersensitive information such as login credentials, financial details, andpersonal data. Cybercriminals sell this data to other malicious actors foridentity theft, financial fraud, or other illicit activities.

This is an outcome of the ecosystem’s resilience, largely supported by the migration of users15. Correspondingly, the multihoming activity is a mechanism that contributes to the ecosystem’s resilience. Because they are already active in more than one market, the migration cost for the multihomers is usually smaller compared to that for non-multihomer users, especially for sellers, that need to rebuilt their reputation23. The period of dominance by Silk Road is unique, because the ecosystem structure is effectively composed of and dominated by a single market, expressed by a market share equal to one, as shown in Fig. After the shutdown of Silk Road, in the last quarter of 2013, the ecosystem evolves to a structure where several markets coexist.



