That’s why the user shouldn’t be negligent about the web pages viewed and purchases made on the...
wpadmin
The acos() function returns the arccosine of a FLOAT in radians. The log10() function returns the common...
Whether you’re looking for the latest cypher tor trends or seeking to replace a trusted household item,...
They use unique addresses that end with .onion, which are not available on search engines. Cybercriminals on...
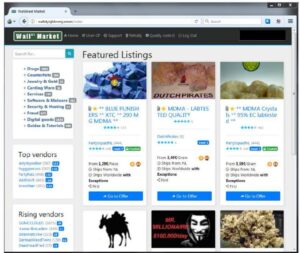
Other than the Silk Road 2.0, similar marketplaces also emerged, but they all went down sooner or...
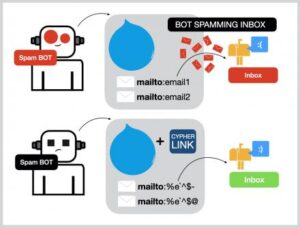
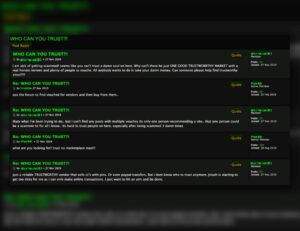
Good community forums are the most reliable sources of verified access information. Using these details to steal...
Abacus employs AES-256 encryption with mandatory PGP for vendor comms, ensuring data privacy. Multi-layered DDoS protection countered...
Adopting simple rules and habits, such as using different passwords for different accounts and employing a password...
The Silk Road was a famous dark web marketplace where users could buy and sell goods and...
The eDarkTrends NER algorithm was designed to identify and group opioid drug mentions into higher-level classes (e.g.,...