Similarly, there is no unique choice for the classification parameters or ground truth for fitting them. In...
Unlike VPNs, which also provide anonymity, it reroutes the users’ traffic through a network of nodes rather...
Buyers and sellers used wallets controlled either directly or through third-party mixers and exchanges. Vendors on Incognito...
They’d secretly been running Hansa for a few weeks, harvesting user data and hijacking the site’s inbuilt...
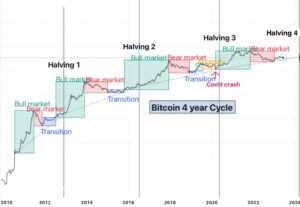
{The best month for the darkweb market was this June, when the value of brokered sales peaked...
Its Tor routing keeps a 92% uptime, with downtimes tied to seller syncs, not breaches, showing active...
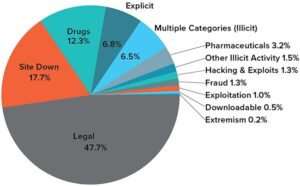
Some are looking for illegal stuff they can’t buy elsewhere, like drugs or counterfeit documents. In line...
With the above dangers, it’s imperative to tread carefully as you step into the dark web. Its...
“Exit scams” occur when marketplace operators suddenly shut down, stealing funds from escrow wallets and disappearing. Dark...
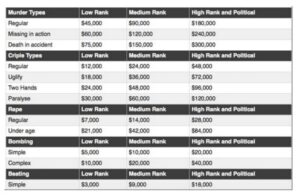
The continuous expansion of available items ensures that users can always find what they are looking for,...