Buyers and sellers used wallets controlled either directly or through third-party mixers and exchanges. Vendors on Incognito...
markets
Its Tor routing keeps a 92% uptime, with downtimes tied to seller syncs, not breaches, showing active...
While the Tor Project relies mainly on a centralized directory of relays, I2P uses a distributed dynamic...
To access this marketplace, you must register, but before that, you must verify yourself as a human...
A VPN protects your connection against everyone, not just your ISP and the authorities. It encrypts your...
I started to purchase controlled substances solely from newcomers and in four years never received only two...
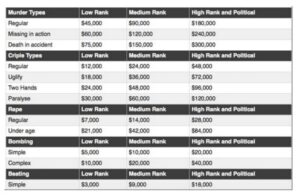
Dark web vendors sell stolen personal identifying information (PII), stolen credit card numbers with verification codes, fraudulent...
Based in Switzerland, ProtonMail is an encrypted email service that is very popular with cryptocurrency enthusiasts. Wasabi...
Axis Intelligence provides dark web surveillance solutions that help businesses identify leaked credentials, fraud attempts, and malware...
Mega clearly dominated the realm of wholesale drug purchases, capturing 51.9% of that segment. Darknet market role...