
While Tor offers a degree of anonymity, combining it with a VPN like Forest VPN adds an extra layer of security. Recon was developed by Hugbunt3r, a prominent figure within the well-known dark web platform, Dread. Its purpose is to function as a repository enabling users to explore items from various sellers across diverse marketplaces on the dark web. Users can also view individual profiles of vendors and marketplaces, providing information such as ratings, alternate links, the number of listings, and the percentage of uptime. On the other hand, the dark web is a subset of the deep web that requires special software to access. The most common method to access the dark web is through the Tor network, which uses the Tor Browser.

Darknet Search Engines:
Tor and I2P are the two commonly used tools for accessing the dark web to provide anonymity. For instance, services like ProtonMail and SecureDrop (mentioned above already) have hidden sites for their users who live in countries with high levels of censorship. The anonymity provided by onion routing comes at the cost of slowing your internet considerably. As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls. The Dark Web is the part of the deep web that is not indexed by search engines, like Google or Bing. For this reason, you cannot browse through these sites using your default search engine.
Forums And Communities

Once a buyer makes a payment, it’s usually held in escrow until they receive what they bought. Typically, you can find dark web URLs through forums, databases, or by talking to others who frequent those sites. There are currently several online darknet markets, but they tend to be incredibly volatile due to government intervention. If you do need to access a dark web website for legitimate reasons, you can check directories like The Hidden Wiki to help find options. Using Forest VPN is essential for protecting your privacy while browsing these sites. It encrypts your connection, ensuring anonymity as you explore the dark web.
Can I Access onion Sites On My Mobile Device?
- It’s also advisable to use antivirus software and avoid downloading anything.
- It was initially created to provide additional security and eliminate cryptocurrency theft.
- Otherwise, the first node in the onion relay system sees your real IP address, which can be used to locate you and unveil your identity.
- Individual sites on the dark web look much like they do on the regular web, though a lot of them are a bit more rough around the edges.
- Be aware, however, that there are sites for absolutely everything, from the benign to the very illegal.
- Although profiting from pirated copyrighted material is unethical and illegal, there are some exceptions to using copyrighted material, such as a “private study” provision under UK law.
To access onion sites, users need a stable internet connection and the Tor browser. ProPublica was the first online publication to win a Pulitzer prize. They were also the first to host a .onion site to make their content accessible to everyone everywhere, regardless of censorship or anti-journalist laws in certain countries. SecureDrop is a really awesome Tor service that can be used to share information without revealing your identity. Many news publications (including many of the ones listed above) use SecureDrop on their .onion sites. But anything that’s against the law on the regular web or offline is also illegal on the dark web.
About Onion(s) And The Dark Web

Otherwise, the first node in the onion relay system sees your real IP address, which can be used to locate you and unveil your identity. Apart from the dark web markets that are operating online today, some raided platforms influenced many markets. Some are looking for illegal stuff they can’t buy elsewhere, like drugs or counterfeit documents. While browsing online, you might have noticed that the websites you are visiting have URLs starting …
Used in with a dedicated private browser, DuckDuckGo is a powerful search engine and a potent privacy tool. Dark web browsers and search engines do a lot of work to mask user identities, but you’re never completely untraceable. Not to mention that anonymity safeguards won’t protect you from other threats like hacking and malware. DuckDuckGo is built into the Tor browser, making it a convenient option for looking up dark web websites.

Abacus Market
Create new anonymous accounts when necessary, using temporary email services. I also recommend covering your webcam and disabling location services before accessing .onion sites. Onion sites, named for their ‘.onion’ domain suffix, are accessible only via the Tor browser.
Staying Safe On The Dark Web
To get on the dark web, you need a browser built for the job, and the best in the business is Tor. Tor is a browser engineered for extra security and privacy, and can be used to navigate the normal, surface web as well as the dark web. It blocks trackers, prevents user fingerprinting, encrypts data, and reroutes your browsing so no one can see where in the world you are.
Always tread carefully whenever crowdsourcing information on how to navigate the dark web. That’s why they’re often a popular means of communication among activists, whistleblowers, political organizers, and ethical hackers. Starting with ProPrivacy and now Proton, Douglas has worked for many years as a technology writer. During this time, he has established himself as a thought leader specializing in online privacy. Douglas was invited by the EFF to help host a livestream session in support of net neutrality.
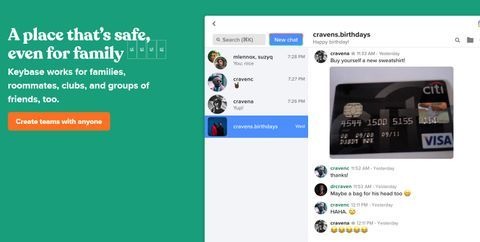
- Keybase is an exciting identity service that aims to make it easy for you to link the presence of your online identities together in a cryptographic way.
- The onion site is especially beneficial for people in regions with heavy censorship or restricted access to media.
- You should stay away from everything labeled “porn”, “card skimming services”, “PayPal hacks”, “firearms”, “real fake IDs and passports”.
- Note that engaging with the content in any way is not only distressing but could also put you at legal risk.
Also, you can set a strong password to protect your message and choose how long it will take to expire. The Tor Metrics is a good place to get more information about the Tor project. It collects data from the public Tor network and archives historical data of the Tor ecosystem. In most cases, whistleblowers have sensitive information about the government or a company.
The site is strongly resistant to hackers and encrypts your data in transit as well as the rest. The starting point for many people’s journeys into the darker corners of the Internet, “the Hidden Wiki” is a vast repository of many of the more popular dark websites on Tor. It can be a bit of a Wild West, but if that’s the case, then The Hidden Wiki is like a frontier town, where there’s at least some semblance of order. National Cooperative Bank does not endorse and is not responsible for their content, links, privacy or securities policies.
Afterwards, your request will be matched with the appropriate website. Tricky, but effective; that’s why it’s, by far, the best method to access dark web content. Unlike regular browsers that directly connect to websites via your ISP’s DNS, Tor anonymizes your journey by routing your request through several relays before reaching its destination.
By doing these things, you make your Tor Browser look like every other Tor Browser, minimizing websites’ ability to fingerprint(new window) you. Because Tor is very slow, many dark web-only websites avoid complex designs and fancy graphics to deliver a faster experience. Dark websites, on the other hand, can only be accessed with Tor (or something similar). Despite multiple attempts to break Tor (some of which have had some partial success), it remains by far the best way to achieve true anonymity on the internet. In this article, we look at some of the best legitimate Tor websites on the dark web.



