
People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web. Established in 2012, the platform is a time capsule that collects snapshots of websites. These onion addresses will remain online even if the original page disappears. It also keeps the graphical copy and text of the page for better accuracy.
Taking the necessary precautions makes tracing your activities on the dark web difficult. Although the Tor browser has sufficient encryption, combining it with a VPN offers better protection. However, you should not see it as an opportunity to engage in illegal activities to avoid trouble with authorities. You should never use your personal information on the dark web anywhere else in your life.
For Sale On The Dark Web
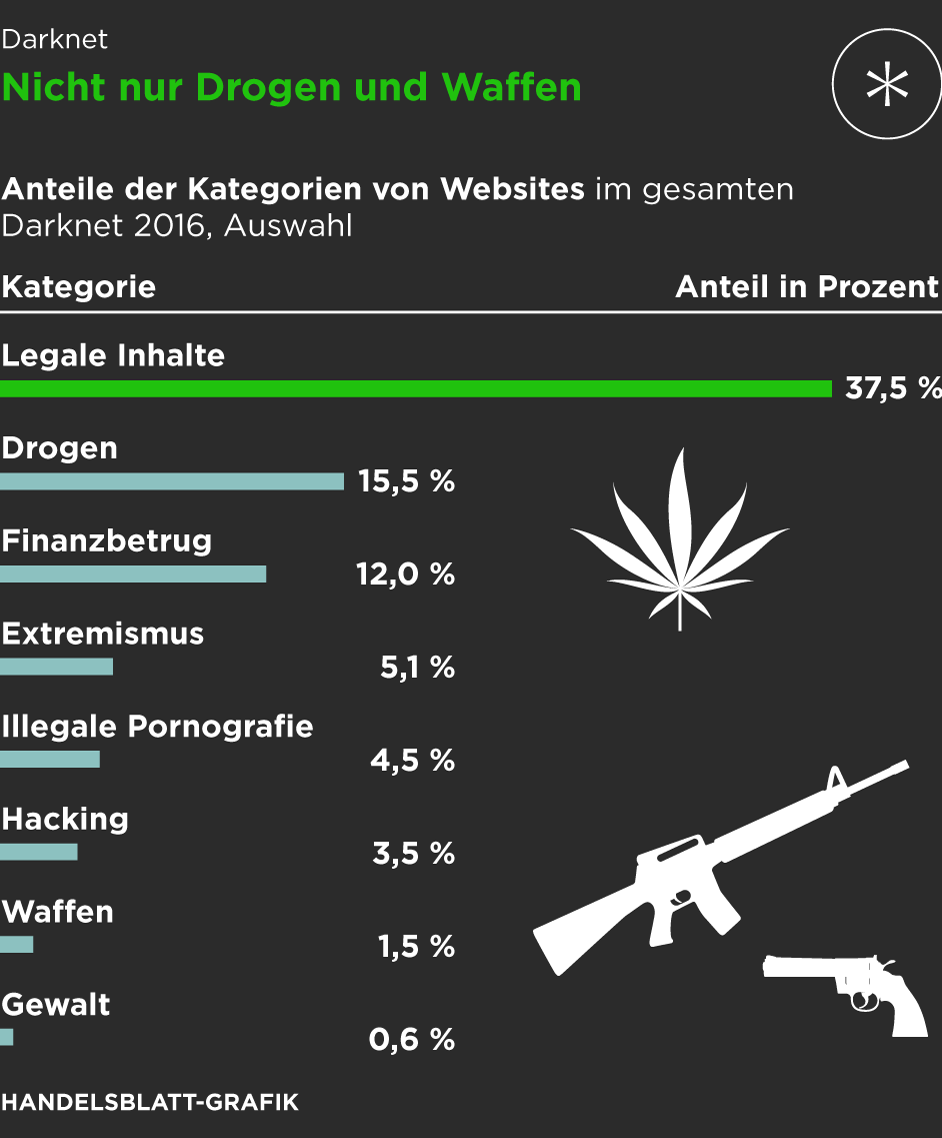
The MITRE ATT&CK framework provides a comprehensive view of adversary tactics. Singularity™ Threat Intelligence provides insights into adversary tactics and helps mitigate these risks before they impact your organization. They use pseudonymous wallets, privacy coins (like Monero), mixers, chain-hopping, and non-KYC platforms to obscure transaction trails. Ransomware and cryptocurrency-based crimes saw a significant increase in 2023, with a nearly $176 million rise compared to 2022. Further market diversification occurred in 2015, as did further developments around escrow and decentralization.
How To Access The Dark Web: Step-by-Step Tutorial (and A Few Words Of Caution)
The US Supreme Court has indicated that even casual browsing could lead to legal consequences. As I’ve previously said, it’s a good idea to keep your interactions with the dark web to a minimum, unless you can absolutely trust the people you’re dealing with. You’ll often see a sign in stores that says “look, don’t touch,” and it’s not a bad adage to bear in mind as you navigate around the dark web. Also, anybody can sign up to sell or buy; you just need to make an account through the open entry registration form. For example, if you’re browsing the internet in your London home, you won’t want to be tracked back there.
- One of the central76 discussion forums was Reddit’s /r/DarkNetMarkets/,777879 which has been the subject of legal investigation, as well as the Tor-based discussion forum, The Hub.
- Since you’re accessing the Dark Web markets, you must be aware of the dangers you could face.
- It encrypts your traffic at the entry node and changes your IP address.
- Specialized search engines, directories, and wikis can help users locate the data they’re looking for.
- Perform image selection captcha, rotate the image correctly, and identify missing letters in the URL and “BlackOps onion” to ensure security.
The general volatility of darknet markets has led to calls for further decentralization of transactions to protect both buyers and vendors. If cryptocurrency is held in a customer account on a darknet platform, it’s always at risk if a site shuts down. You can use dark web search engines to find some helpful dark websites. You can also find secure email services, independent journalism platforms, and even the dark web Wiki.
Darknet Markets Norge
HSI was one of the primary agencies on the Silk Road investigation that revealed large-scale illegal drug and contraband smuggling through the U.S. The investigation eventually led to activity taking place on Darknet marketplaces. “This case, along with Black Market Reloaded, represented a new and evolving area, cyber investigation, for law enforcement that continues to this day,” said DAD Lechleitner. Put simply, the deep web is all the information stored online that isn’t indexed by search engines. You don’t need special tools or a dark net browser to access most of the deep web; you just need to know where to look. Specialized search engines, directories, and wikis can help users locate the data they’re looking for.
Ways Agentic AI Is Transforming Cybersecurity
Dark web search engines exist, but even the best are challenged to keep up with the constantly shifting landscape. The experience is reminiscent of searching the web in the late 1990s. Even one of the best search engines, called Grams, returns results that are repetitive and often irrelevant to the query.
Things You Must Do Before You Access The Dark Web
The Department of Justice noted that DisrupTor was initiated after “U.S. Claire Georges, a spokeswoman for Europol, confirmed to me recently that DisrupTor was “entirely designed around” that first cache of information from CyberBunker’s servers. One of the clues unearthed by the trawl of CyberBunker’s servers was related to the ownership of DarkMarket. In May, 2020, an online-crime unit in the northern German city of Oldenburg was asked to investigate.
(NOT) Lost In Translation – Why Your Language Doesn’t Matter To Cybercriminals
Keybase also offers extremely user-friendly secure chat and file-sharing services through its app. Based in Switzerland, ProtonMail is an encrypted email service that is very popular with cryptocurrency enthusiasts. The process costs a fee, but unlike other “tumbler” or “mixing” services, there is no risk that Wasabi or any of its users could scam you out of your coins. One of the most popular ways to get around the dark web is not to use a search engine at all. Just like in the old days of the internet, the dark web maintains numerous indexes of sites, like The Hidden Wiki. Unlike Ahmia and Haystak, however, DuckDuckGo doesn’t search .onion sites.
Features That Make WTN Market A Secure Platform

Dark markets include features similar to those found in legitimate e-commerce platforms, such as product listings, user reviews, ratings, and customer support. These features help create a sense of ‘trust’ among users, even in the criminal ecosystem. Freshtools is a unique marketplace in that it does not only provide the stolen data, but it allows criminals to purchase MaaS which can cause further damage to the victims.
Meanwhile, Facebook also offers dark web access to their social network. NordVPN offers a 30-day, no-risk trial subscription when you sign up on this page. This provides a full month’s access to all of the features of the #1 VPN for the Dark Web. This is an excellent way for Dark Web users to provide additional privacy protection when accessing the Dark Web.
Radar Rundown The dark web consists of many websites with uncensored information; choose a suitable … There are several other browsers you can use, such as Freenet and I2P, but Tor is the most recommended option. Unfortunately, the platform was shut down in 2013 after an extensive investigation that was spearheaded by US Senator Charles Schumer. The closure led to the arrest of the platform’s founder Ross Ulbricht.
The surface web (often referred to as the “visible web”) is the portion of the web available to the general public and indexed in the standard web search engines such as Google, Bing, and Yahoo. Pixel Privacy believes in digital privacy and does not believe in using it for heinous and/or illegal activities, and so the focus of this article will be on legal activities. The content of all these pages is stored on Google’s servers, but it’s mostly outdated, old content; smartphone app content; journals; court records; private social media profiles, and much more. STYX market features a robust verification process, making it look more exclusive.
Legitimate Use Cases For The Average User

This increases the accessibility and sophistication of cyber threats, with far-reaching consequences for businesses. To secure against these risks, organizations invest in robust cybersecurity strategies, conduct regular security assessments, and educate employees to recognize and mitigate threats. Silk Road was a notorious cyber black market for illicit goods and the first dark web market of the internet era. Launched in 2011 and shut down by the FBI in 2013, Silk Road paved the way for today’s underground world of dark web marketplaces. Then, get powerful cybersecurity software to keep yourself safer wherever you go online.



