
Silk Road, which emerged in 2011, combined TOR and bitcoin to become the first known darknet market. The market was eventually seized in 2013, and the founder, Ross Ulbricht, was sentenced to two life sentences plus 40 years without the possibility of parole. Ulbricht’s hefty prison sentence did not appear to have the intended deterrent effect. Multiple markets emerged to fill the void and, in doing so, created a thriving ecosystem profiting from stolen personal data. Forum administrators were less than convinced, however, demanding that Yale Lodge pay its stolen data suppliers manually until the “technical issues” were resolved. Elihu Yale refused, but said that customer deposits for those who wanted to purchase stolen cards were functioning as normal.
- They can then sell the account credentials to a buyer who can log in and drains the funds, or the vendor can transfer the requested amount of money from the victim’s account to the buyer’s account.
- Customers can set up notifications for specific spending thresholds, international transactions, or card-not-present (online) transactions, enabling prompt detection of unauthorized activity.
- Founded in 2019, DarkMarket acted as an illicit marketplace where drugs, counterfeit money, stolen credit card data, anonymous SIM cards.
- Prepare to be astounded, as we unveil the chilling reality that lies beyond the bright glow of your credit card statement.
Magnetic Stripe Data Dumps
The illegal internet market specialized in the sales of drugs, counterfeit money, stolen or forged credit card information, anonymous SIM. Last week, I found out that my credit card information was stolen and The AlphaBay Market has darknet markets 2021 a feature called CC Autoshop that allows. A Russian group has reportedly released data on some 1 million credit cards on the dark web, making it available for sale to criminals. The marketplace has been around since May 2021 and is available on a Tor channel too.
Why You Need Automated Dark Web Monitoring
The popular Silk Road was the first dark web marketplace that you could only access via the Tor Browser. The global cost of cybercrime has been on an alarming rise with the estimated loss to be in billions of dollars, with some reports indicating that the overall loss could be in trillions. A large portion of this cost can be attributed to the fraud conducted due to stolen PII data, some of which we have covered in this blog. For example- In Asia, Australia has been impacted the most due to identity crimes with an estimated loss of AUD $2.2 billion annually.
Threat Actor Profiles
Some dark web marketplaces even host content that’s not just illegal but extremely harmful, so it’s really important to understand the risks before diving in. Others are looking for stolen data, hacking services, or even banned books and political content. Some are looking for illegal stuff they can’t buy elsewhere, like drugs or counterfeit documents. The story of dark web marketplaces kicks off with Silk Road, launched in 2011. It was the first big site where people could anonymously buy drugs using Bitcoin, and it gained a lot of attention, until it was shut down by the FBI in 2013.
Indicators Of Compromise In Threat Intelligence
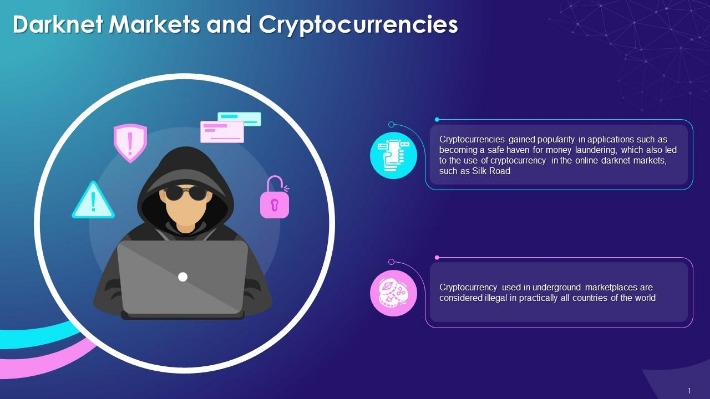
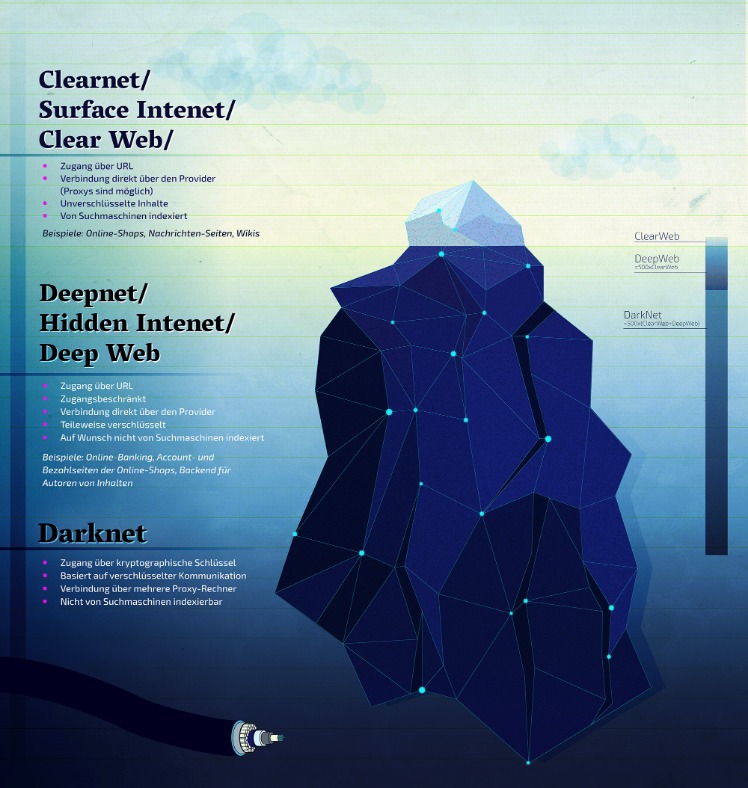
Another key distinction is that access to darknet markets requires the use of special software such as the Onion Router, or TOR, which provides security and anonymity. The stolen data supply chain begins with producers—hackers who exploit vulnerable systems and steal sensitive information such as credit card numbers, bank account information, and Social Security numbers. Next, the stolen data is advertised by wholesalers and distributors who sell the data.
Stolen Data Ecosystem
The darknet is basically an overlay network that exists within the internet and can only be accessed with specific configurations, software, and usually uses certain customized communication protocols. The dark web is only accessible through specific software like Tor (The Onion Router). Also, while this huge portion of the internet has a reputation as home to nefarious activities like hacking and drug trafficking, it also harbors legitimate activities like journalists and whistleblowers. In October 2021, White House Market – the largest darknet market of its kind – announced that it would shut down. It’s also the latest in a growing list of criminal marketplaces to have voluntarily retired in the last six months. These groups often originate from leaked credit card credentials, which have become a common phenomenon, particularly in the past months.

Next, we extracted information about stolen data products from the markets on a weekly basis for eight months, from September 1, 2020, through April 30, 2021. We then used this information to determine the number of vendors selling stolen data products, the number of stolen data products advertised, the number of products sold, and the amount of revenue generated. The first category includes classic marketplaces, which serve as one-stop shops for a wide range of illegal goods. These platforms sell everything from drugs and fake IDs to weapons and hacking tools, resembling a digital black-market bazaar. Many banks now offer virtual credit cards—temporary digital card numbers linked to your primary account. Use virtual cards for online shopping, as these numbers are single-use or short-term, limiting potential exposure if compromised.
Darknet Market Bible
In addition to these types of listings, there are other free tools usually available on credit card sites. These tools include for example different types of checkers, which assist threat actors in verifying whether the stolen card information they possess is valid and can be used to make unauthorized purchases. While there are legitimate products and services in the darknet markets, often, these markets deal with illicit goods and services like drugs, fake documents, and hacking services. Their presence can make you wonder why darknet markets and not just the regular online stores.
Online Analytical Processing, or OLAP, is a powerful technology for data discovery, including… B1ack’s Stash’s sudden rise in popularity has been met with mixed reactions from dark web users. Most comments range from negative to neutral, while very few users gave clearly positive endorsements based on their site experience. Use this guide to learn how to easily automate supply chain risk reports with Chat GPT and news data.
This entire process used to be called “Carding,” a term that has become a key part of the cybercriminal playbooks. “Closures and seizures of carding sites in 2022 have so far accounted for almost 50% of sales in the dark web stolen credit card market,” Elliptic said. “Darknet markets remain highly lucrative enterprises, and if anything, the retirements could give operators the confidence that they can operate a successful market and make their fortunes – without being apprehended.” These platforms serve as hubs for cybercriminals to easily buy and sell compromised payment card details, including credit card numbers, CVV codes, expiry dates, and cardholder information.
Cartel Darknet Market
In January 2021, after a sustained international law enforcement campaign led by the FBI and supported by Interpol, Joker’s Stash closed operations permanently. Prior to its closure, Joker’s Stash hosted over 40 million stolen credit card records and generated hundreds of millions of dollars in illicit revenue. Although the anonymous administrator behind the marketplace was never publicly identified or arrested, authorities seized multiple servers and cryptocurrency wallets, significantly disrupting global carding networks.
Conclusion And Recommendations For Preventing Credit Card Fraud
Carders target sites without these protections, and some vendors even sell lists of “cardable” sites for a few dollars. Manual monitoring of the dark web is inefficient and risky due to the sheer volume of data involved. This early detection allows organizations to identify and respond to threats quickly, reducing the chances of unauthorized access, financial loss, or damage to brand reputation. The market is especially well-known for providing access to freshly compromised data, often obtained from recent breaches and stealer logs. This platform has rapidly become a key player in the fraud market, trading in PII and SSH credentials while making use of both the clear and dark web.



