Sellers often need to pay a deposit to prove they’re serious, and they build their reputation through positive reviews. In 2019, there were approximately 8,400 active sites on the dark web, selling thousands of products and services daily. As of 2020, nearly 57% of the dark web was estimated to contain illegal content, including violence and extremist platforms. Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools.
Community Resilience And Knowledge Sharing

With ZeroBin, you can easily exchange encrypted messages within the dark web. With 256-bit AES encryption, this platform enforces its two-fold service of secure messaging and zero logs of your activity. In addition, Haystak offers a premium plan that allows deeper search, email alerts, and access to historical content. ProPublica is a prominent investigative journalism platform on the regular and dark web. This duality allows users to choose whether to access the platform openly or anonymously. If we need a website to get links to other hidden sites, we will choose Hidden Wiki.
Why You Need Automated Dark Web Monitoring
The future of darknet drug trade lies in its ability to adapt to technological advancements while maintaining the core principles of privacy and reliability. These features collectively make the darknet a reliable environment for drug trade in 2025, offering users a seamless and secure experience. Additionally, the integration of Bitcoin and other cryptocurrencies has streamlined transactions, eliminating the need for traditional banking systems. This not only enhances privacy but also reduces the risk of financial tracking.
We Helped Patch A Chromium Bug That Could Leak Your Real IP — Here’s How
Social engineering attacks leverage trust, fear, curiosity, or urgency to trick users into revealing sensitive information, transferring funds, or compromising their anonymity. By learning to recognize these ploys and adopting defensive habits, you can significantly reduce the risk of becoming a victim. As we mentioned above, when you connect to Tor your data first goes through an entry node, which can see your IP address. By connecting to a VPN before using Tor, you mask your real IP address before it reaches this entry node, adding an extra layer of security and anonymity. The Dutch national police have made their onion site function as a billboard, warning all would-be criminals on darknet marketplaces to think twice about their actions.
What Is The Dark Web & How To Stay Safe
Tor markets and darknet sites maintain robust security protocols, ensuring user privacy and transaction integrity. Abacus Market appeared on the scene in 2021 and quickly became one of the heavyweights among English-speaking markets on the dark web. The categories are well organized, ranging from drugs and fraud to digital products, guides, and malware.What really sets it apart is its focus on security and usability. It supports PGP encryption, two-factor authentication (2FA), alerts against fake sites (antiphishing), and a verification system for sellers. Its interface is easy to navigate, and it has a reliable escrow system, as well as allowing payments with Bitcoin and Monero. All of this has made it one of the most reliable markets still active in 2025.
The dark web in 2025 still holds power, but only for users who browse smartly. Stick to verified directories, question everything, and always put your privacy first. For safety in transactions, here’s why cryptocurrency is preferred on the dark web. Monero’s ring signatures, stealth addresses, and RingCT ensure untraceable trades. In 2025, 95% of markets prefer XMR over BTC’s public ledger, with transaction volume up 60% since 2023.
Poker Day Designs Unique Poker Tees, Accessories, And Hoodie Goodies™
For users looking to preserve their privacy, knowing how to find real dark web links and access dark web sites that are safe in 2025 is essential. In an age of surveillance and data leaks, these hidden networks still offer something the surface web often can’t — freedom and anonymity. On this darknet markets list you will find only current onion links to dark web markets. Only reliable and trusted onion darknet market links are located here. The functionality of the links is constantly checked, not the workers onion links are removed. The darknet has become a cornerstone for secure and reliable drug trade, offering users a platform that prioritizes privacy and efficiency.
Specialized Data Repositories
One genuine exception is a site called Keybase, which helps you securely share files and chat online. It uses public key cryptography to ensure the chats remain anonymous to everyone except the participants. Proton further provides access over the Tor network through its customized onion address.
Vice City Market
- By approaching this hidden corner of the internet with informed caution and ethical awareness, you can navigate it more safely and responsibly.
- Whether you’re new to the dark web or a vet who’s seen it all, you’ll find something here to chew on.
- You can use Dread to learn which dark net markets are reputable and their locations.
- By leveraging automated dark web monitoring, organizations can mitigate risks, and take preventive measures before the leaked data is exploited.
This means your activities cannot be traced or your browser history exposed. In due course, the framework was remodeled and made public as a secure browser. Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. An easy way to find content on the dark web is to receive a link from someone who already knows about it. Some whistleblowers and journalists use these portals to safely leak information, especially when a source requires complete privacy.
- Careful though, because many ‘users’ reported malicious links and redirects while perusing Sci-Hub.
- Dark web community channels are always evolving to ensure that they evade law enforcement agencies.
- Also, even in countries where accessing the dark web is legal, it’s still against the law to use or host sites that promote criminal activities.
- High-rated vendors often gain more visibility, which incentivizes others to maintain high standards.
- Having JavaScript enabled on the dark web can cause havoc because it can reveal your IP address to your website.
- It’s made up of forums, marketplaces, and websites you can’t find with a Google search and requires specialized software to access, such as the Tor Browser.
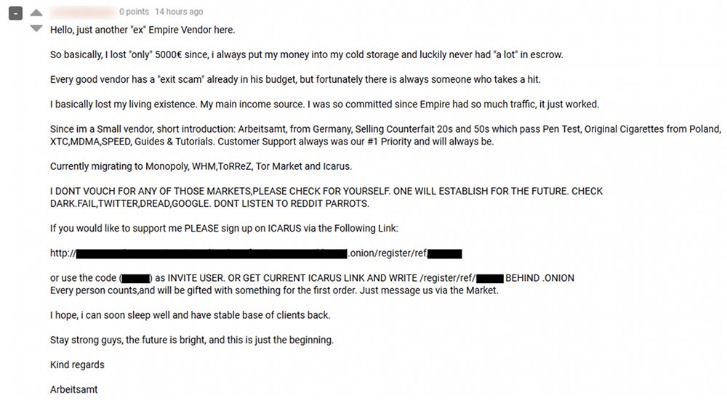
What makes Dread trusted is its long-standing PGP-verifiable admin presence and active moderation against scams and phishing. It’s also hosted through resilient infrastructure to fight against DDoS attacks and frequent takedown attempts, helping it remain a reliable platform for uncensored discussion. In 2025, the terms “dark web links” and “dark web sites” have become more familiar to everyday internet users, but the concepts behind them are still widely misunderstood.
Dark Web Sites Name List: Where To Find Secure Marketplaces
The website has an advanced search filter and an easy-to-use interface, which makes it easy to find what someone is looking for. It will offer you an additional layer of encryption to access the deep parts of the internet. So, conducting dark web social hubs’ monitoring can offer significant intelligence for cybersecurity professionals and law enforcement. That way, they can easily combat criminal and illicit activities and also help to stop data breaches and several other potential malicious attacks.
These platforms rely on advanced encryption and decentralized systems to ensure anonymity and reliability for both buyers and sellers. The darknet has become a cornerstone for secure and reliable drug trade, offering users unparalleled privacy and efficiency. These platforms rely on advanced encryption and decentralized infrastructure, making them highly resistant to external interference. ProtonMail offers a .onion version of its encrypted email service, giving users end-to-end privacy with access through Tor. Mail2Tor is a more anonymous option, offering a simple inbox interface without storing logs or metadata. These services are ideal for exchanging messages without exposing your identity, whether you’re speaking to journalists, forums, or personal contacts in high-surveillance regions.



