
This browser enables access to websites with .onion domain extensions, which are specific to the Tor network. These addresses cannot be resolved by conventional DNS servers, contributing to the hidden nature of darknets. We web-parsed the Hydra darknet drug marketplace using Python code.
The History Of Darknet Marketplaces
Laws vary by jurisdiction, so readers should always check their local regulations before attempting to access the dark web. Because Google and Bing don’t index onion sites, you’ll need dedicated search engines to navigate the dark web. A few well-known ones make finding content easier, though quality and safety can vary.
- Activists, journalists, and whistleblowers use the dark web to communicate safely without fear of retribution.
- Stolen data remains a top-selling commodity, with new breaches appearing almost daily.
- If you purchase something from such shops and make payment through conventional payment methods like your bank transfer, credit/debit card, or PayPal, you can be caught easily and face legal consequences.
- You can use dark web monitoring services or free tools like haveibeenpwned.com to check if your email, passwords, or other personal data have appeared in known dark web data breaches or dumps.
Cybersecurity Awareness Explained: Importance & Best Tips 2025
As with all powerful technologies, the dark web and its markets reflect both the best and worst of human intentions. Silk Road quickly grew into the largest darknet market, handling hundreds of millions in transactions. But in 2013, law enforcement traced Bitcoin activity, monitored DPR’s forum posts, and exploited server vulnerabilities to identify Ross Ulbricht. He was arrested in a San Francisco library while logged in as site admin.
At the same time, the study’s findings represent a specific time frame and may not capture evolving trends in drug use and market dynamics. By following these important do’s and don’ts, you’re arming yourself with the tools to navigate this intricate landscape of Dark Web more securely. Remember, whether you’re a seasoned user or a curious beginner, adhering to these guidelines will help protect your privacy and ensure a safer experience on the Darknet market.
Offering books for free, shadow libraries face the morality question of copyright vs. access to information and knowledge. Just Another Library is one such service, with a wealth of books covering computer programming, science, and niche hobbies (sailors’ knots, anyone?). It also offers works of art, course material, and audiobooks for download. Following the NYT, the BBC launched a dark web “mirror” of their international edition in 2019. Note that some features of the normal website are not available on the .onion version, including BBC iPlayer.
Tips For Safe Browsing:
Compared to other regions, Krasnodar’s rate of 22.50 g of opiates per 100,000 people is exceptionally high. Figure 4 illustrates the distribution of opiates by region, setting the stage for the subsequent discussion on regional public health impacts. Regional distribution of all drugs for sale presented on Hydra, in grams per 100,000 population in Russia. Data visualization and imagining approaches were used to help interpret the results of this study step.

The Dark Web: Risks And The Role Of Standards

The VPN encrypts your connection and masks your IP address, providing an extra layer of security. Many operators have since moved to accepting only Monero (XMR),” Chainalysis added. While DeFi adoption among darknet vendors is growing, it has not replaced centralized exchanges as the primary laundering method. However, the trend is clear—illicit actors are expanding their strategies, forcing enforcement agencies to evolve their tracking methods to keep pace with increasingly sophisticated laundering techniques. Experienced blogger with a strong focus on technology, currently advancing towards a career in IT Security Analysis. I possess a keen interest in exploring and understanding the intricacies of malware, Advanced Persistent Threats (APTs), and various cybersecurity challenges.
Related Articles From The Safe Browsing Section

Torch is one of the oldest and most popular onion search engines on the dark web, serving over 80,000 requests per day. Torch is funded primarily through advertising—purchased in BTC, of course—which is why you’ll find the front page blanketed with old-school banner ads of dubious origins. Your real information could be exposed at these nodes, allowing third parties to intercept your dark web activity. That’s why we recommend connecting to VPN before accessing Tor—VPN encryption protects your data, and changing your IP adds an extra layer of privacy to protect you. However, any illegal activities conducted on the dark web, such as purchasing illicit goods or engaging in criminal behavior, are still punishable by law.
It has some advertisements on its home page, but they’re for popular searches and services to help get you started. Ahmia is a search engine for .onion sites — you search for a keyword and Ahmia retrieves relevant results. I tested it 10+ times, and it always provided me with accurate search results.
Best Privacy Protection Apps For Ultimate Anonymity And Security
It has been estimated that a large percentage of dark web traffic is related to illegal pornography that includes underage victims. As you are now familiar with the three different sections within the entire world wide web, let’s take a closer look at how you can access the dark web anonymously. We’ve also previously mentioned the “dark users” that use the dark web for illegal reasons, but the less said about them, the better. Those who access the dark web do so via the Tor (The Onion Router) browser. Absolutely no one knows who’s surfing on the dark web, who is selling, who is buying or anything like that – as long as you take the correct safety and online privacy precautions.
Award Winning Cybersecurity
If the person tracking you is very advanced and has unlimited resources, they could conceivably de-anonymize you when you make certain mistakes, like downloading files or enabling scripts. Don’t be fooled into going to a malicious clone site that is designed to extract your information. Downloading anything online can be dangerous, let alone the hidden internet. With the growing abilities of corporations to monitor and collect our data, the core principle upon which the dark web exists is now more relevant than ever. Though it still requires being routed through Tor (it is not a deep web browser by itself), it provides a clean, quick, and privacy-respecting base to use for your anonymous browsing sessions. Its main appeal is that it offers more privacy and supports legacy Firefox add-ons.
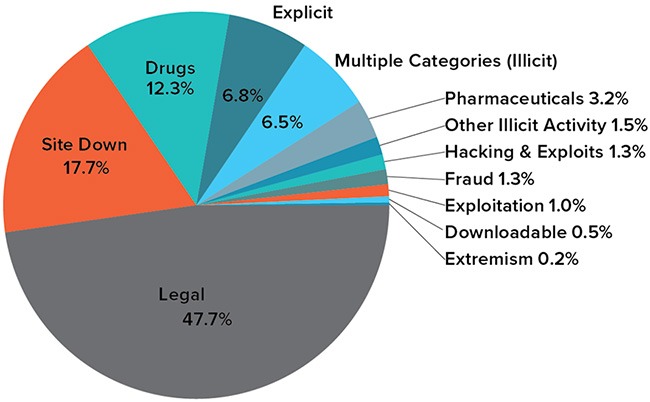
It features over 40,000 listings including narcotics, counterfeit items, hacking tools, and stolen data. The marketplace is well-known for its bug bounty programs and robust security mechanisms, including mandatory 2FA. Perhaps the best-known thing you can buy on the Dark Web is information collected in what seems like the almost daily data breaches we read about in the news. That information can include checking and credit card account numbers, social security numbers, and other sensitive information. To access darknets, users typically need to download and configure the Tor Browser; a modified version of Mozilla Firefox that routes all traffic through the Tor network.
Best Dark Web Browsers Today – Detailed List
They employ various techniques, such as tracking and infiltrating dark markets, developing advanced threat intelligence, and enhancing international cooperation. As darknets and dark markets continue to evolve, understanding their dynamics and implications is crucial for fortifying the cybersecurity defenses of individuals, organizations, and nations in the digital age. Darknets and dark markets have fueled the growth of cybercrime, provided a marketplace for cyber threats, and expanded the attack surface for malicious actors.



